Rule Sets and Rule Set Groups
Rule Sets
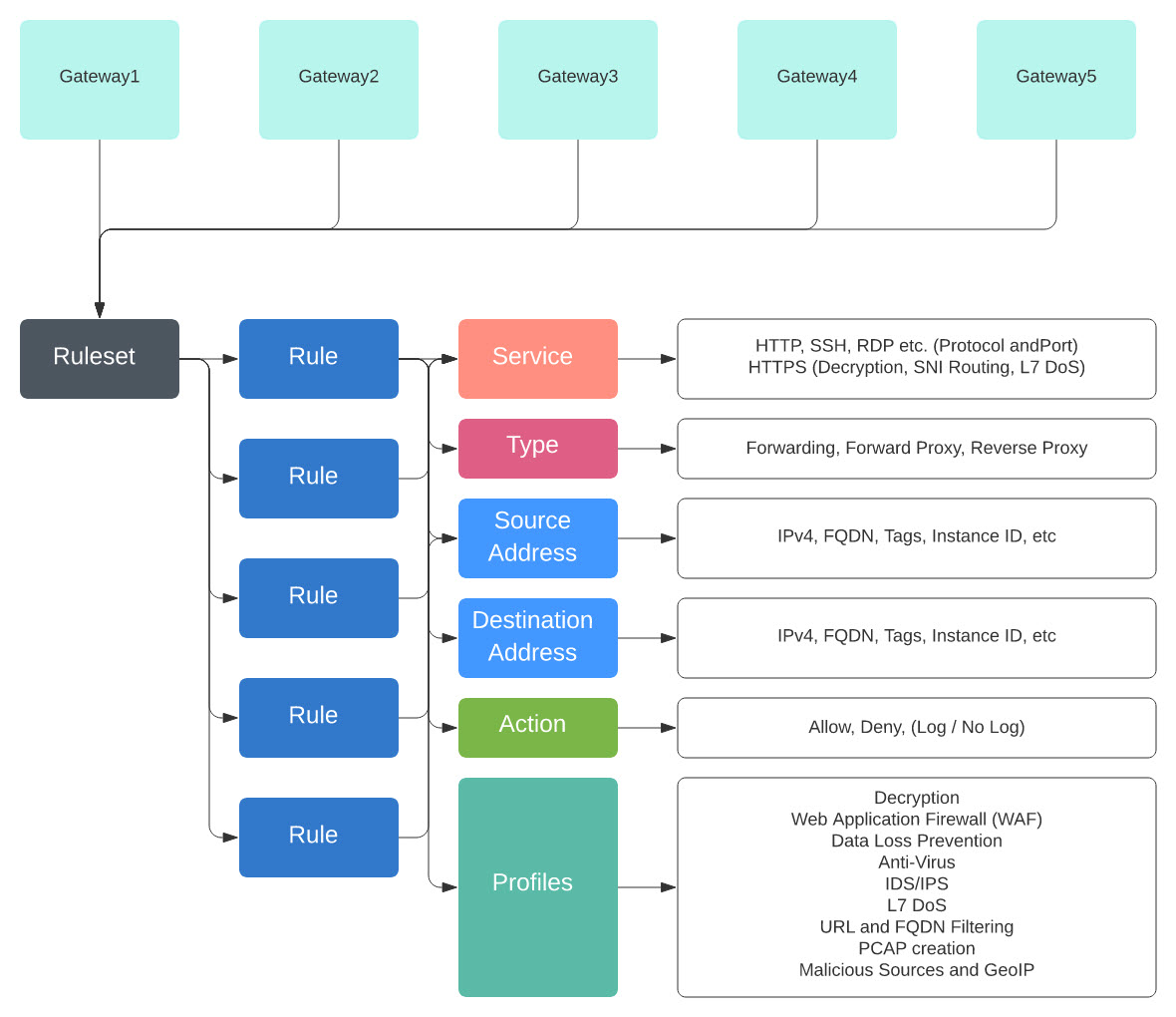
Rule sets consist of a set of rules that define a segmentation and advanced security policy that are applied to a set of one or more gateways to accommodate application and workload protection. The rules are organized as a priority list where traffic is processed by a matched rule, a general action is taken to allow or deny, and further inspection is accommodated through advanced security.
Rule sets must be associated with at least one Multicloud Defense Gateway. The following limitations apply to all rule sets:
-
Rule sets are cloud agnostic and can be applied to one or more gateways operating across multiple cloud environment.
-
A gateway can only be associated with a single rule set, although more than one rule set can be applied using a rule set group.
-
Rules within a rule set can use discovered cloud asset information to form a dynamic policy, or a policy that adapts in real time to changes.
-
A rule set can include rules that only apply to specific cloud accounts and/or cloud regions, although the rule set is applied to gateways that cross cloud environments. Here is an example:
-
A dynamic tag-based address object used in a rule within a rule set that is applied to two gateways across two clouds can resolve to a set of IP addresses that are associated with a gateway in one cloud, while resolving to a different set of IP addresses that are associated with a gateway in another cloud.
-
-
Rule sets can be created from the page or from within the gateway creation workflow. The following diagram is of a a single rule set applied to multiple gateways:
Another supported use case is of multiple rule sets associated with multiple gateways.
Policy Rule Set Groups
A policy rule set group is a collection of standalone rule sets. Users can combine multiple standalone rule sets into a policy rule set group and associate the group to one or more Multicloud Defense Gateways. Policy rule set groups allow organizations to separate policies in an organized fashion and combine them to an overarching policy.
Note |
|