Change the Manager Access Interface from Management to Data in a High Availability Pair
You can manage the FTD from either the dedicated Management interface, or from a data interface. If you want to change the Cisco Security Cloud Control access interface after you added the device to Security Cloud Control, follow these steps to migrate from the Management interface to a data interface. To migrate the other direction, see Change the Manager Access Interface from Data to Management in a High Availability Pair.
Initiating the Security Cloud Control access migration from Management to data causes the Security Cloud Control to apply a block on deployment to the FTD. To remove the block, enable Security Cloud Control access on the data interface.
Note | Unless stated otherwise, perform all steps mentioned in this section only on the active unit. Once the configuration changes are deployed, the standby unit synchronizes configuration and other state information from the active unit. |
See the following steps to enable Security Cloud Control access on a data interface, and also configure other required settings.
Before you begin
Model Support—Threat Defense
Procedure
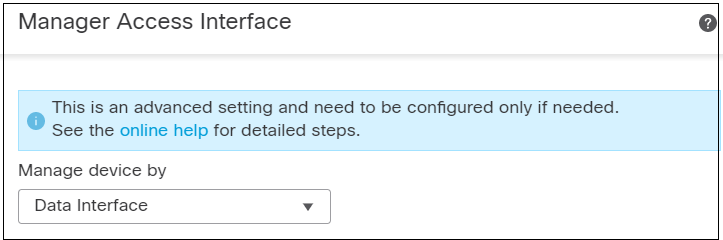
Step 1 | Initiate the interface migration. | ||
Step 2 | Enable Security Cloud Control access on a data interface on the page. See Configure Routed Mode Interfaces.You can enable Security Cloud Control access on one routed data interface. Make sure this interface is fully configured with a name and IP address and that it is enabled. | ||
Step 3 | Make sure the FTD can route to the Security Cloud Control through the data interface; add a static route if necessary on . See Add a Static Route. | ||
Step 4 | (Optional) Configure DNS in a Platform Settings policy, and apply it to this device at . DNS. DNS is required if you use DDNS. You may also use DNS for FQDNs in your security policies. | ||
Step 5 | (Optional) Enable SSH for the data interface in a Platform Settings policy, and apply it to this device at . See SSH Access. SSH is not enabled by default on the data interfaces, so if you want to manage the FTD using SSH, you need to explicitly allow it. | ||
Step 6 | Deploy configuration changes. The Security Cloud Control will deploy the configuration changes over the current Management interface. After the deployment, the data interface is now ready for use, but the original management connection to Management is still active. | ||
Step 7 | At the FTD CLI (preferably from the console port), set the Management interface to use a static IP address and set the gateway to use the data interfaces. configure network {ipv4 | ipv6} manual ip_address netmask data-interfaces
We recommend that you use the console port instead of an SSH connection because when you change the Management interface network settings, your SSH session will be disconnected.
| ||
Step 8 | When the deployment completes around 90 percent, the new management interface takes effect. At this stage, you must re-cable the FTD so that the Security Cloud Control reaches FTD on the data interface and completes the deployment successfully. After you re-cable, the deployment may fail if it timed out before re-establishing the management connection to the new interface. In that case, you must reinitiate the deployment after re-cabling for a successful deployment.
| ||
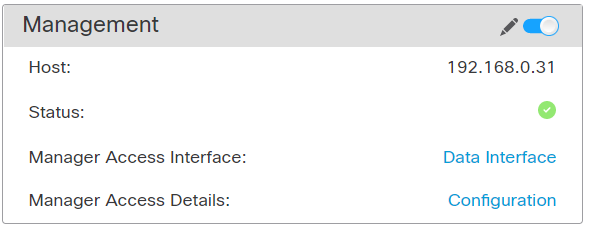
Step 9 | Ensure the management connection is reestablished. In Security Cloud Control, check the management connection status on the page. At the FTD CLI, enter the sftunnel-status-brief command to view the management connection status. The following status shows a successful connection for a data interface, showing the internal "tap_nlp" interface. 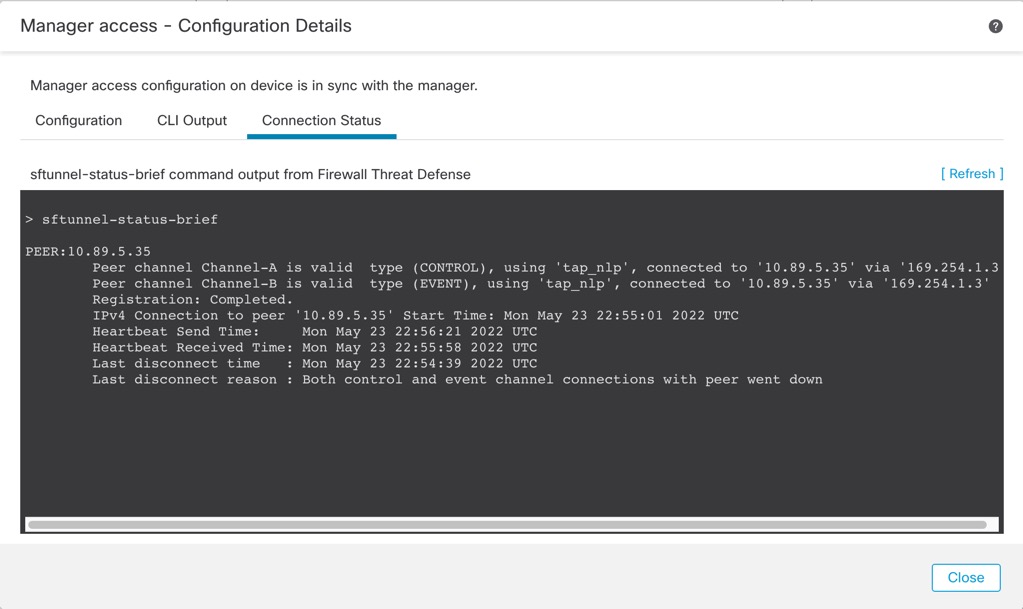
If it takes more than 10 minutes to reestablish the connection, you should troubleshoot the connection. See Troubleshoot Management Connectivity on a Data Interface. |